Kerberos in MAC OS X
Kerberos authentication allows the computers in same domain network to authenticate certain services with prompting the user for credentials. MAC OS X comes with Heimdal Kerberos which is an alternate implementation of the kerberos and uses LDAP as identity management database.Here we are going to learn how to setup a kerberos on MAC OS X which we will configure latter in our application.
Installing Kerberos
In MAC we can use Homebrew for installing any software package. Homebrew makes it very easy to install the kerberos by just executing a simple command as given below.brew install krb5Once installation is complete, we need to set the below export commands in user's profile which will make the kerberos utility commands and compiler available to execute from anywhere.
Open user's bash profile:
vi ~/.bash_profileAdd below lines:
export PATH=/usr/local/opt/krb5/bin:$PATH
export PATH=/usr/local/opt/krb5/sbin:$PATH
export LDFLAGS="-L/usr/local/opt/krb5/lib"
export CPPFLAGS="-I/usr/local/opt/krb5/include"
Creating kerberos configuration
Now we need to create kerberos configuration which will be used during the setup of our installed kerberos. In this configuration we will setup few things like, domain names, KDC setup, logging, default keytab etc. Kerberos authentication looks up for the /etc/krb5.conf file which is default kerberos configuration location in MAC OS and we will create this file if it does not exist. If this file already exists then we can use the existing kerberos also for the modification. Here I am considering the situation when this file is not available and we need to create it.To create our kerberos configuration, we will use below user and domain.
User: macuser Domain: myserver.localhostTo configure above domain, we need to add below configuration in /etc/hosts file.
127.0.0.1 myserver.localhost MYSERVER.LOCALHOST
/etc/krb5.conf
Execute below command to create the file.sudo vi /etc/krb5.confPut below code in this file and save it. In below code we also set the default encryption code supported. Also we set whether weak encryption is allowed. We have set the keytab, admin keytab location and KDC database also here. Same database will be created and setup the users & domain also.
[libdefaults]
default_realm = MYSERVER.LOCALHOST
default_keytab_name = file:/Users/macuser/krb5/conf/krb5.keytab
default_tkt_enctypes = aes256-cts-hmac-sha1-96
default_tgs_enctypes = aes256-cts-hmac-sha1-96
allow_weak_crypto = true
forwardable=true
dns_lookup_realm = false
dns_lookup_kdc = false
[logging]
default = FILE:/Users/macuser/krb5/logs/krb5kdc.log
admin_server = FILE:/Users/macuser/krb5/logs/kadmind.log
kdc = FILE:/Users/macuser/krb5/logs/krb5kdc.log
[realms]
MYSERVER.LOCALHOST = {
kdc = myserver.localhost
database_name = /Users/macuser/krb5/db/principal
admin_server = myserver.localhost
admin_keytab = file:/Users/macuser/krb5/conf/kadm5.keytab
}
MYSERVER = {
kdc = myserver.localhost
database_name = /Users/macuser/krb5/db/principal
admin_server = myserver.localhost
admin_keytab = file:/Users/macuser/krb5/conf/kadm5.keytab
default_domain = myserver.localhost
}
[domain_realm]
.localhost = MYSERVER.LOCALHOST
myserver.localhost = MYSERVER.LOCALHOST
Create database
To create the database we need to create below directory structure which we have mentioned in our kerberos configuration file./Users/macuser/krb5/db/ /Users/macuser/krb5/conf/ /Users/macuser/krb5/logs/We need to execute below command to create the database.
kdb5_util create -r MYSERVER.LOCALHOST -sYou will see the similar output where you can see the database location which we configured in kerberos configuration file.
Loading random data Initializing database '/Users/macuser/krb5/db/principal' for realm 'MYSERVER.LOCALHOST', master key name 'K/M@MYSERVER.LOCALHOST' You will be prompted for the database Master Password. It is important that you NOT FORGET this password. Enter KDC database master key: Re-enter KDC database master key to verify:
Creating principle, policies and keytab file
Execute below command to open the kadmin console in given directory. If you want to use specific encryption type while configuring database and keytab, then open kadmin with same command by specifying "-e" parameter with comma separated encryption typescd /Users/macuser/krb5/conf/ kadmin.localNow execute below commands in kadmin console to create policies. Policy creation is not necessary but it is always helpful to manage users using policies.
addpol users addpol admin addpol hostsExecute below commands in kadmin console to create principles.
addprinc -policy users macuser addprinc -policy admin macuser/admin addprinc -randkey -policy hosts host/myserver.localhost addprinc -randkey HTTP/myserver.localhostExecute below commands in kadmin console to create keytab files.
ktadd -k krb5.keytab host/myserver.localhost ktadd -k krb5.keytab HTTP/myserver.localhost ktadd -k krb5.keytab macuser ktadd -k kadm5.keytab kadmin/admin kadmin/changepw
Verifying and initializing keytab
Exit the kadmin console by typing "quit" and execute below command to check the keytab entries.klist -e -k -t krb5.keytabIt will given you below output:
Keytab name: FILE:krb5.keytab KVNO Timestamp Principal ---- ----------------- -------------------------------------------------------- 2 12/29/19 20:40:17 host/myserver.localhost@MYSERVER.LOCALHOST (aes256-cts-hmac-sha1-96) 2 12/29/19 20:40:17 host/myserver.localhost@MYSERVER.LOCALHOST (aes128-cts-hmac-sha1-96) 2 12/29/19 20:40:32 HTTP/myserver.localhost@MYSERVER.LOCALHOST (aes256-cts-hmac-sha1-96) 2 12/29/19 20:40:32 HTTP/myserver.localhost@MYSERVER.LOCALHOST (aes128-cts-hmac-sha1-96) 2 12/29/19 20:40:43 macuser@MYSERVER.LOCALHOST (aes256-cts-hmac-sha1-96) 2 12/29/19 20:40:43 macuser@MYSERVER.LOCALHOST (aes128-cts-hmac-sha1-96)Now execute the same command on "kadm5.keytab" to check the admin entries. Below is the output.
Keytab name: FILE:kadm5.keytab KVNO Timestamp Principal ---- ----------------- -------------------------------------------------------- 2 12/29/19 20:40:55 kadmin/admin@MYSERVER.LOCALHOST (aes256-cts-hmac-sha1-96) 2 12/29/19 20:40:55 kadmin/admin@MYSERVER.LOCALHOST (aes128-cts-hmac-sha1-96) 2 12/29/19 20:40:55 kadmin/changepw@MYSERVER.LOCALHOST (aes256-cts-hmac-sha1-96) 2 12/29/19 20:40:55 kadmin/changepw@MYSERVER.LOCALHOST (aes128-cts-hmac-sha1-96)Now check if you have read permission for other users also on both the keytab files (created above). If not then please update the permission on them. Post that, please execute below commands in given sequence, to start your kerberos.
krb5kdc kadmindFinally, execute below command to initialize your keytab with given user.
kinit macuser@MYSERVER.LOCALHOST -kt krb5.keytabIt will ask for the password, we set during principal creation.
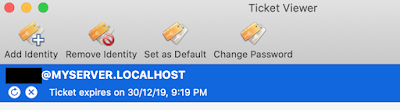
Now open the "Ticket viewer" and you will see similar to below screen for your initialized user.
You can check my another post on implementation of Kerberos authentication using Spring boot and SPNEGO API.
https://www.thetechnojournals.com/2019/12/integratedkerberos-authentication-using.html
I am trying to follow the instruction to set up my Kerberos server on mac OX, I have faced two issues:
ReplyDelete1) ```kdb5_util create -r MYSERVER.LOCALHOST -s```, after you input the password, I will get error
```kdb5_util: Can not fetch master key (error: No such file or directory). while initializing the Kerberos admin interface```
2) ```cd /Users/macuser/krb5/conf/
kadmin.local
```
I will have the problem that kadmin.local is trying to open the database `/usr/local/Cellar/krb5/1.17.1/var/krb5kdc/principal`, and this will get a result No such file or directory while initializing kadmin.local interface
Is there anything wrong? Any suggestion will be appreciated
You getting these issues as your database couldn't created and then latter it failed during initialization due to same issue.
DeleteSeems, you have not defined below database setting in your "/etc/krb5.conf" file which specifies the desired location for database.
database_name = /Users/macuser/krb5/db/principal
If you don't want to use above setting and want to use default location for database then please make sure that you have below folder hierarchy, if not then please create the folders. Folder hierarchy for database must be present with both custom and default database location.
/usr/local/Cellar/krb5/1.17.1/var/krb5kdc/
Then try to create database using kdb5_util.
Hey i read your blog and find it very helpful for me because i was looking for these type of content online.
DeleteReasons Why To Hire A Bodyguard in London, UK:| Spetsnaz Security International Fidel Matola
https://www.spetsnazsecurityinternational.co.uk/reasons-to-hire-a-london-bodyguard.html
Thanks for your reply.
ReplyDeleteI have define the database setting in the config file, however, it seems like kadmin.local cannot find the default real I config in the krb5.conf, I have to use `sudo kadmin -r MYSERVER.LOCALHOST` to let it know where is the path of the database.
For the first issue, I just simply add "sudo" in front of the command to execute, then the issue is gone.
Cool.
DeleteHi,
ReplyDeletei've follow all the steps you provided, but when i run the `kdb5_util create -r MYSERVER.LOCALHOST -s` command, after typing the master key password i got the following error:
kdb5_util: Key table file '/usr/local/Cellar/krb5/1.17.1/var/krb5kdc/.k5.MYSERVER.LOCALHOST_tmp' not found while storing key
Warning: couldn't stash master key.
kdb5_util: Can not fetch master key (error: No such file or directory). while initializing the Kerberos admin interface
What am i doing wrong? Do you please have any suggestion?
Thanks in advance
I tried your previously suggestion: create `/usr/local/Cellar/krb5/1.17.1/var/krb5kdc/` path. This solved my issue. Now i have another one. When i run `kadmin.local` i got the following error:
Deletekadmin.local: unsupported command
Any suggestion?
Thanks in advance
Seems your krb5 sbin is not set on environment's path and not able to find this command. You can set it by exporting location "/usr/local/opt/krb5/sbin" in PATH variable. If this location is not available then you can export location "/usr/local/Cellar/krb5/1.17.1/sbin" in PATH variable. Other way is to execute the command by prepending it with actual location, for example "/usr/local/opt/krb5/sbin/kadmin.local".
DeleteFirst of all, thanks for you support!
DeleteMy krb5 sbin path is already setup as environment variable.
However using kadmin.local inside "/usr/local/Cellar/krb5/1.17.1/sbin" folder everything works fine.
Thanks again!
while running "sudo kadmind" , I get the below error : kadmind: Cannot open /usr/local/Cellar/krb5/1.18.2/var/krb5kdc/kadm5.acl: No such file or directory while initializing ACL file, aborting
ReplyDeleteHello, I am facing the same problem mentioned in the before comment, I did all the steps and everything worked fine until there, after run sudo kadmin the next error is displayed: kadmind: Cannot open /usr/local/Cellar/krb5/1.18.2/var/krb5kdc/kadm5.acl: No such file or directory while initializing ACL file, aborting
ReplyDeleteCan you please give me an idea on how to solve this?
Please try to create below folder hierarchy.
Delete/usr/local/Cellar/krb5/1.18.2/var/krb5kdc/
Please try to create below folder hierarchy.
ReplyDelete/usr/local/Cellar/krb5/1.18.2/var/krb5kdc/
I have the same problem when i try to start kadmind I am getting the same error sudo kadmind
ReplyDeletekadmind: Cannot open /usr/local/Cellar/krb5/1.18.2/var/krb5kdc/kadm5.acl: No such file or directory while initializing ACL file, aborting . However the directory exists, it is just that there is no acl file in there. Any ideas?
Never mind, it expects a predefined acl file. A simple touch /usr/local/Cellar/krb5/1.18.2/var/krb5kdc/kadm5.acl suffices to get the server started. Apparently this is a plain text file with some access control lists, the user has to define himself!
Deletehttps://web.mit.edu/kerberos/krb5-1.12/doc/admin/conf_files/kadm5_acl.html
Another problem now... kinit myuser@MYSERVER.LOCALHOST -kt krb5.keytab results in an error kinit: Client 'werpu@MYSERVER.LOCALHOST' not found in Kerberos database while getting initial credentials. The db exists the keytab file has the user and the user exists on macos, i am somewhat puzzled why this happens.
DeleteHi there and thanks a lot for your tutorial.
ReplyDeleteI followed each of the steps you recommended but when i enter :
kdb5_util create -r MYSERVER.LOCALHOST -s
I get :
zsh: command not found: kdb5_util
I looked up on the internet and didn't find anything besides checking the $PATH
So my $PATH is as this :
/usr/local/bin:/usr/bin:/bin:/usr/sbin:/sbin:/Library/Apple/usr/bin
If you mind helping me out I would be so gratefull !
Cheers :)
First go inside the folder (cd /Users/macuser/krb5/db/) and then execute kdb5_util create -r MYSERVER.LOCALHOST -s
DeleteIt worked for me. Hope it might help you.
@Aprajita didn't work for me
DeleteThanks for a very helpful tutorial, it worked for me like a charm. The only missing detail I found is you never mention where to place the keytab files and looking at the krb5.conf they should be placed in the file:/Users/macuser/krb5/conf/ folder. The other items which caused problem for me was missing kadm5_acl.html file. Initially I added it as an empty file but later I found out it really needs to be setup correctly so one can use kadmin. Adding a short section explaining that detail would be very helpful for beginners like myself.
ReplyDeleteGreat article. I followed the instructions on Mac Big Sur and it complaint about pkinit authentication with the following message from the krb5kdc log "preauth pkinit failed to initialize: PKINIT initialization failed: No pkinit_identity supplied for realm MYSERVER.LOCALHOST". After trying to set up pkinit the following the official mit documentation it still complaints about the first line that tries to access the MYSERVER.LOCALHOST in the extensions.kdc I've defined. Any help would be highly appreciated!
ReplyDeleteIf you're frantically seeking straight hair, a flat iron feels like the apparent device to grab besides, a good one can aid make your hair smooth, glossy as well as pin-straight. That claimed, if you've found that the process of detangling your hair prior to having to area off your strands and make several passes with a straightener to be a time suck, there's a much easier method to accomplish a flawlessly straight 'do.Visit us for honest review.yourwisepick.com
ReplyDeleteGoogle announced 'Instant Apps' for Android in Google I/O last year. This year, the search giant updated 'Instant Apps' and made it available for developers with gloud games svip mod apk --- so that they can start making them.
ReplyDeleteWeldon. So good article. Also checkout:
ReplyDeleteApkKiss
Crunchyroll Premium Apk Reddit
Crunchyroll Premium Apk
Project QT MOD Apk 13.5 [Unlimited Gems Skills Coins]
Moe Girl Cafe 2 Mod Apk [Money Diamonds Unlocked]
Need for Speed No Limits Mod Apk [Unlimited Money Gold]
Fishing Strike Mod Apk (Unlimited Money & Damage Unlocked)
Great post keep good posting/. you can als visit Alight motion ios download
ReplyDelete
ReplyDeletetopfollow for windows is best app to increase instagram follwer. so visit website and increase your real time follwers
Hi,
ReplyDeletekinit myuser@MYSERVER.LOCALHOST -kt krb5.keytab results in an error kinit: Client 'werpu@MYSERVER.LOCALHOST' not found in Kerberos database while getting initial credentials.
Any ideas how to fix this?
Hi,
ReplyDeletekinit myuser@MYSERVER.LOCALHOST -kt krb5.keytab results in below error
kinit: Client 'macuser@MYSERVER.LOCALHOST' not found in Kerberos database while getting initial credentials
Any ideas how to fix this?
This is the last step to test the flow of kerberos
macOS Monterey may be running it's own KDC, before you run krb5kdc and kadmind - you can disable the built in kdc with: "sudo launchctl unload -w /System/Library/LaunchDaemons/com.apple.Kerberos.kdc.plist"
ReplyDeleteDownload the best quotes and shayari
ReplyDeletehere you can find the best status
ReplyDeleteSoccer Agent Mod Apk has excellent graphics, and an attractive plot, Download Soccer Agent Mod Apk's latest version Free 2022 updated
ReplyDeleteModern Age 2 MOD APK is a geopolitical, economic, and military strategy game. download Modern Age 2 MOD APK President Simulator unlimited money download Modern Age 2 MOD APK
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteThanks for sharing the useful information about set up Kerberos in Mac OS. If you are looking for the leading and reliable Mobile App Development Company In India, then you can go with Lucid Outsourcing Solutions they have team of expertise who have in-hand experience in various technologies.
ReplyDeleteQuite an informative blog! I have found interesting details to read and provide immense knowledge Thanks for the wonderful information. If you are looking for tailor made erp software for your business, book a free consultation Custom ERP Solution
ReplyDeleteelazığ
ReplyDeletebilecik
kilis
sakarya
yozgat
KCTZR2
görüntülüshow
ReplyDeleteücretli show
NED
https://titandijital.com.tr/
ReplyDeletemersin parça eşya taşıma
osmaniye parça eşya taşıma
kırklareli parça eşya taşıma
tokat parça eşya taşıma
MQSN
antep evden eve nakliyat
ReplyDeletebolu evden eve nakliyat
afyon evden eve nakliyat
tekirdağ evden eve nakliyat
artvin evden eve nakliyat
A8N
adana evden eve nakliyat
ReplyDeletebolu evden eve nakliyat
diyarbakır evden eve nakliyat
sinop evden eve nakliyat
kilis evden eve nakliyat
DCELV
adana evden eve nakliyat
ReplyDeleteafyon evden eve nakliyat
istanbul evden eve nakliyat
burdur evden eve nakliyat
gümüşhane evden eve nakliyat
GW4
9F1B7
ReplyDeleteSivas Şehirler Arası Nakliyat
Konya Şehirler Arası Nakliyat
Eskişehir Parça Eşya Taşıma
Bingöl Lojistik
Ardahan Parça Eşya Taşıma
Pursaklar Boya Ustası
Adıyaman Şehir İçi Nakliyat
Çerkezköy Kombi Servisi
Tekirdağ Parke Ustası
C200B
ReplyDeleteVan Şehir İçi Nakliyat
Loop Network Coin Hangi Borsada
Kütahya Evden Eve Nakliyat
Bilecik Lojistik
Antalya Şehirler Arası Nakliyat
Nexa Coin Hangi Borsada
Samsun Lojistik
Pitbull Coin Hangi Borsada
Zonguldak Şehir İçi Nakliyat
14CCA
ReplyDeleteTokat Şehir İçi Nakliyat
Çanakkale Şehirler Arası Nakliyat
Uşak Evden Eve Nakliyat
Bitcoin Nasıl Alınır
Artvin Evden Eve Nakliyat
Tunceli Evden Eve Nakliyat
Amasya Şehir İçi Nakliyat
Sinop Lojistik
Diyarbakır Lojistik
98E20
ReplyDeleteVan Evden Eve Nakliyat
Hakkari Lojistik
Düzce Şehirler Arası Nakliyat
Edirne Parça Eşya Taşıma
Malatya Parça Eşya Taşıma
Amasya Şehir İçi Nakliyat
Çankırı Şehir İçi Nakliyat
Bilecik Şehir İçi Nakliyat
Çerkezköy Kombi Servisi
851CE
ReplyDeleteEtimesgut Boya Ustası
Erzurum Evden Eve Nakliyat
Samsun Evden Eve Nakliyat
Bursa Şehir İçi Nakliyat
Antep Parça Eşya Taşıma
Btcturk Güvenilir mi
Aksaray Şehirler Arası Nakliyat
Kastamonu Evden Eve Nakliyat
Adana Şehir İçi Nakliyat
E32DA
ReplyDeleteYalova Şehir İçi Nakliyat
Yozgat Evden Eve Nakliyat
Kocaeli Evden Eve Nakliyat
Tokat Şehir İçi Nakliyat
Niğde Evden Eve Nakliyat
Casper Coin Hangi Borsada
Trabzon Evden Eve Nakliyat
Ünye Kurtarıcı
Ankara Parke Ustası
49308
ReplyDeleteAnkara Boya Ustası
Çankırı Evden Eve Nakliyat
Uşak Lojistik
Silivri Boya Ustası
Amasya Evden Eve Nakliyat
Ordu Lojistik
Hatay Lojistik
Mersin Şehir İçi Nakliyat
Çanakkale Lojistik
78977
ReplyDeletereferanskodunedir.com.tr
D34F8
ReplyDeletebinance %20 komisyon indirimi
4FAAB
ReplyDelete%20 komisyon indirimi
4FD3F
ReplyDeleteBulut Madenciliği Nedir
Binance Kaldıraç Var mı
Coin Nasıl Çıkarılır
Kripto Para Nasıl Oynanır
Bitcoin Oynama
Binance Nasıl Oynanır
Bitcoin Üretme Siteleri
Kripto Para Kazma Siteleri
Bitcoin Nasıl Para Kazanılır
C814C
ReplyDeletebinance referans kodu
resimli magnet
referans kimliği nedir
binance referans kodu
resimli magnet
referans kimliği nedir
resimli magnet
binance referans kodu
binance referans kodu
8EFDD
ReplyDeletesesli görüntülü sohbet
Kayseri Canlı Görüntülü Sohbet
antep canli goruntulu sohbet siteleri
parasız sohbet siteleri
kadınlarla sohbet et
kastamonu canli sohbet bedava
en iyi rastgele görüntülü sohbet
telefonda görüntülü sohbet
yozgat rastgele görüntülü sohbet ücretsiz
486E5
ReplyDeleteadana sohbet
kadınlarla görüntülü sohbet
parasız görüntülü sohbet uygulamaları
düzce canlı sohbet et
kocaeli en iyi ücretsiz sohbet uygulamaları
edirne görüntülü sohbet odaları
zonguldak mobil sohbet chat
canlı görüntülü sohbet odaları
parasız sohbet
95F3D
ReplyDeleteBee Coin Hangi Borsada
Sohbet
Facebook Grup Üyesi Satın Al
MEME Coin Hangi Borsada
Soundcloud Beğeni Hilesi
Big Wolf Coin Hangi Borsada
Kripto Para Nasıl Üretilir
Kwai Takipçi Satın Al
Kripto Para Üretme Siteleri
4F0D2
ReplyDeletepoocoin
dappradar
dexscreener
eigenlayer
dextools
satoshi
yearn
trezor suite
trezor suite
87DC9
ReplyDeletekripto para nasıl alınır
kantaron sabunu
nar sabunu
lavanta sabunu
papaya meyvesi
filtre kağıdı
zerdeçal sabunu
binance
bitcoin hesabı nasıl açılır
CF2DE
ReplyDeletebitcoin nasıl kazanılır
btcturk
bitcoin seans saatleri
gate io
papaya
binance referans kod
canlı sohbet odaları
bybit
referans kimliği
EFF24
ReplyDeletekripto para haram mı
kripto para kanalları telegram
btcturk
kripto ne demek
kizlarla canli sohbet
bitcoin seans saatleri
güvenilir kripto para siteleri
mobil proxy 4g
probit
6B08D
ReplyDeletemexc
binance
filtre kağıdı
gate io
bitcoin nasıl oynanır
telegram kripto
probit
bitcoin nasıl kazanılır
kripto para telegram
24341
ReplyDeletetürk kripto telegram grupları
kraken
canlı sohbet ucretsiz
coinex
bingx
bitexen
bitcoin seans saatleri
mexc
bitcoin hangi bankalarda var
BF572
ReplyDeleteMarch 2024 Calendar
September 2024 Calendar
binance referans kimliği nedir
referans kod
January 2024 Calendar
April 2024 Calendar
mexc
bitexen
kripto ne demek
4AB9A
ReplyDeleteWordpress Hosting
iç mimar
güneş paneli fiyatları
Home Office İş İlanları
Coin Kazanma
İş İlanları
EBay SEO
ehliyet sınav soruları
Facebook Grup
D9152
ReplyDeletesanal sunucu
güneş paneli
dedicated server
İçerik Editörü
istanbul iç mimar
Residential Proxy Satın Al
Bing SEO
vds
Sosyal Medya İşleri
7BA81
ReplyDeleteİş İlanları
güneş paneli fiyatları
vds satın al
Opencart SEO
jeneratör fiyatları
Wordpress SEO
EBay SEO
Yapay Zeka Siteleri
Offshore Hosting
8E5F2
ReplyDeleteFacebook Takipçi Satın Al
freelance iş ilanları
seo nedir
Home Office İş İlanları
Google Reklam Ajansı
Mobil Uygulamalar
Google Adwords Kupon Satışı
Tarayıcı Oyunları
Oyun Forumu
F9FEB
ReplyDeleteSosyal Medya Ajansı
offshore hosting
IPv6 Proxy Satın Al
Tarayıcı Oyunları
bitcoin forum
Twitter Beğeni Satın Al
Anime Önerileri
ebay seo
metin2 pvp serverler
E3A7D
ReplyDeleteWeb Site Kurma
Opencart SEO
Dizi Önerileri
bitcoin yorum
Bitcoin Forum
Yandex SEO
seo
web tasarım
Pvp Serverler
94E89
ReplyDeleteoffshore hosting
SEO Eğitimi
Wordpress Hosting
seo uzmanı
Knight Online Sunucu Kiralama
Amazon SEO
Proxy Satın Al
SEO
freelance iş ilanları
1CF4D
ReplyDeleteTanıtım Yazısı
Web Site Kurma
Facebook Para Kazanma
SMM Panel
Youtube Kanal Satın Al
Telegram Reklam Verme
Wordpress SEO
Sanal Sunucu
kitap önerileri
1EAA2
ReplyDeleteBch Coin Yorum
Imx Coin Yorum
Bitcoin Son Dakika
Kava Coin Yorum
Sushi Coin Yorum
Loka Coin Yorum
Gtc Coin Yorum
BTC Yorum
Near Coin Yorum
C6F68
ReplyDeleteBitcoin Forum
Astr Coin Yorum
Api3 Coin Yorum
Gala Coin Yorum
Avax Coin Yorum
Link Coin Yorum
Forth Coin Yorum
Stmx Coin Yorum
Ocean Coin Yorum
0D87F
ReplyDeleteXec Coin Yorum
Glm Coin Yorum
Bitcoin Forum
Porto Coin Yorum
BTC Son Dakika
Theta Coin Yorum
Chz Coin Yorum
Sys Coin Yorum
Bico Coin Yorum
B3B03
ReplyDeleteücretli show whatsap
BD40F
ReplyDeletesanal şov
EE5E6
ReplyDeletesanal canlı şov
CD7C3
ReplyDeletewhatsapp görüntülü şov
114C5
ReplyDeletewhatsapp görüntülü show
F4629
ReplyDeletegörüntülü show
DCEC3740A5
ReplyDeletesex hattı
sohbet hatti
cam show
görüntülü seks
cam şov
seks hattı
görüntülü sex
sohbet hatti
görüntülü şov
6F20187A00
ReplyDeletegörüntülü şov
sex hattı
cam show
sohbet hatti
sohbet hatti
cam şov
sanal sex
görüntülü sex
görüntülü seks
F595D8ACBC
ReplyDeletewhatsapp görüntülü şov
skype show
ücretli show
cam show
görüntülü show
telegram show
whatsapp görüntülü show güvenilir
görüntülü şov
telegram görüntülü şov
BC39D80705
ReplyDeletecam show
whatsapp görüntülü şov
whatsapp ücretli show
canli web cam show
canli cam show
şov
cam şov
telegram show
ücretli show
65C29C7951
ReplyDeletedegra
cobra vega
kaldırıcı
themra macun
novagra
performans arttırıcı
kamagra
vigrande
lifta
6FF484336A
ReplyDeletegreen temptation
fx15
ücretli show
şov
skype şov
görüntülü şov
kaldırıcı
novagra
geciktirici
3757584F01
ReplyDeleteücretli şov
stag
görüntülü şov
sinegra
cobra vega
delay
ücretli show
degra
sertleştirici
F16B48F214
ReplyDeletesildegra
cialis
bufalo içecek
geciktirici jel
maxman
stag
kaldırıcı hap
delay
bayan azdırıcı damla
E905F1F504
ReplyDeleteücretli şov
geciktirici jel
themra macun
ücretli show
viga
cialis
görüntülü şov whatsapp numarası
canli web cam show
performans arttırıcı
1B7E26B6C0
ReplyDeletemaxman
vega
bufalo içecek
whatsapp görüntülü şov
sinegra 100 mg
cam şov
kaldırıcı hap
lady era hap
novagra hap
E61C442F72
ReplyDeletethemra macun
lifta
görüntülü şov
telegram show
maxman
whatsapp görüntülü show güvenilir
görüntülü şov whatsapp numarası
geciktirici jel
cialis
E57B01AF6D
ReplyDeletetiktok türk beğeni
3F9FF440F8
ReplyDeleteucuz beğeni
A323813E90
ReplyDeletetiktok düşmeyen takipçi
D9DD13C07D
ReplyDeletedüşmeyen takipçi
Pubg New State Promosyon Kodu
Free Fire Elmas Kodu
Erasmus Proje
Coin Kazan
MFF Kupon Kodu
Danone Sürpriz Kodları
Eti Mutlu Kutu Kodları
M3u Listesi
6720C7C213
ReplyDeleteAnadoluslot Giriş
Anadoluslot Giriş
Anadoluslot
Anadoluslot Güncel Giriş Adresi
Trwin Giriş
Trwin
Trwin
Trwin Giriş Adresi
Trwin
A0D7273D56
ReplyDeleteTelegram Airdrop Botları
Telegram Para Kazanma Grupları
Telegram Para Kazanma Grupları
Yeni Telegram Madencilik Botları
Telegram Güvenilir Coin Botları
F97E84FCEC
ReplyDeleteMadencilik Botları
Telegram Madencilik
Telegram Para Kazanma
En İyi Telegram Farm Botları
Güvenilir Telegram Farm Botları
4AE6B39737
ReplyDeletemmorpg oyunlar
sms onay
mobil ödeme bozdurma
takipçi satın alma
-
B50F9211CA
ReplyDeletemmorpg oyunlar
anında sms onay
mobil ödeme bozdurma
twitter takipçi satın alma
-
48A88906FA
ReplyDeletemmorpg oyunlar pc
anında sms onay
mobil ödeme bozdurma
takipçi satın alma
-
EBB24A3446
ReplyDeletemmorpg oyunlar
ucuz sms onay
güvenilir mobil bozum
en iyi takipçi satın alma sitesi
-
E736C3E61A
ReplyDeletekiralık hacker
kiralık hacker arıyorum
kiralık hacker
hacker arıyorum
kiralık hacker
B470C7AD6D
ReplyDeletekiralık hacker
kiralık hacker arıyorum
kiralık hacker
hacker arıyorum
kiralık hacker
ReplyDeleteGünlük yaşamda yeni bilgiler öğrenmek ve kendimizi geliştirmek adına çeşitli kaynaklara ihtiyaç duyarız. Bu noktada, ilgimizi çeken kitapları seçerken dikkatli olmak önemlidir. Özellikle kitap önerileri sayesinde, farklı tarzlarda ve konularda detaylı tavsiyeler bulabiliriz. Böylece, okuma alışkanlığımızı güçlendirebilir ve daha geniş bir perspektif kazanabiliriz.